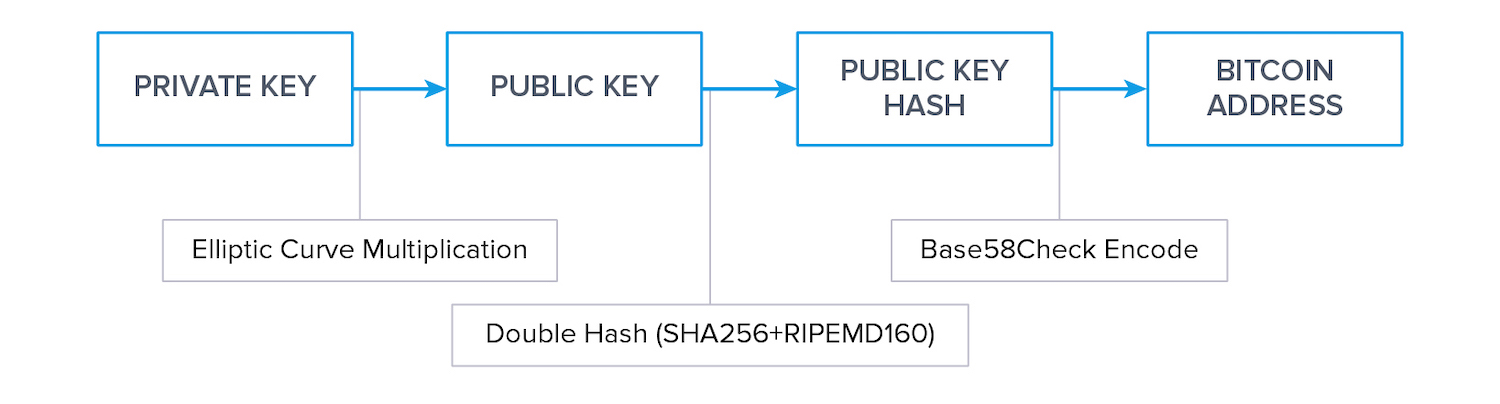
Bitcoin 101 - Elliptic Curve Cryptography - Part 4 - Generating the Public Key (in Python) - YouTube

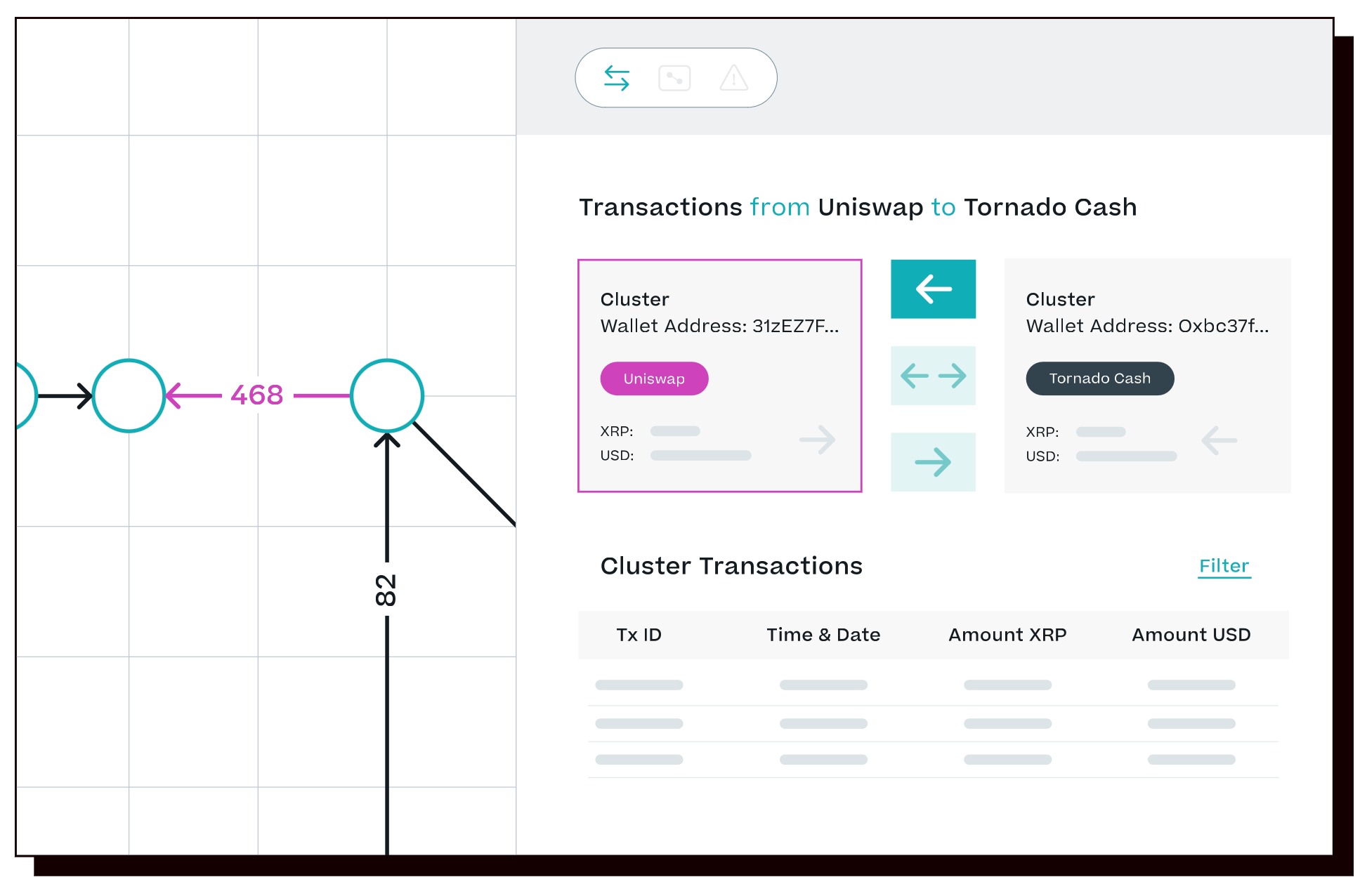
Elliptic says 22% of bitcoins from Twitter hack were likely sent to a Wasabi Wallet address for mixing
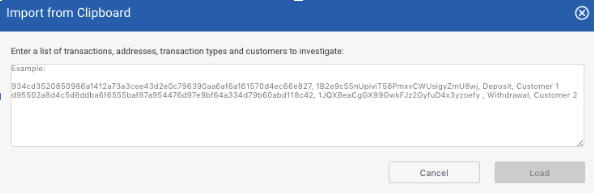
CoolBitX and Elliptic Release Sygna Bridge Wallet Address Filter For Private Wallet Transaction Discovery - Sygna
Elliptic Identifies 'Several Hundred Thousand Crypto Addresses' Tied to Russia-Based Sanctioned Actors – Bitcoin News

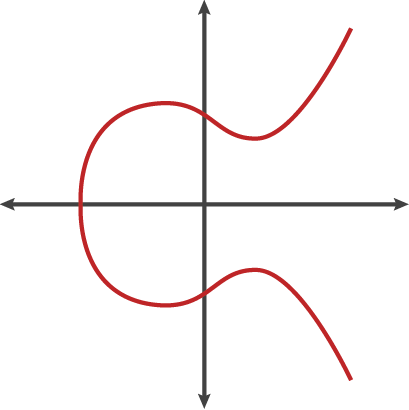
The Ubiquity of Elliptic Curves Joseph Silverman (Brown University) MAA Invited Address Baltimore – January 18, ppt download

Maximillian Engelen on LinkedIn: #ftx #hack #crypto #eth #btc #finance #renbridge #sbf #blockchain #aml
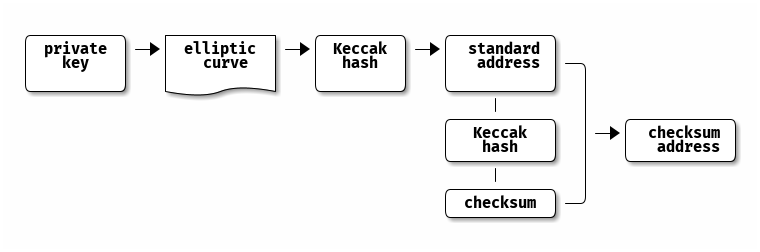
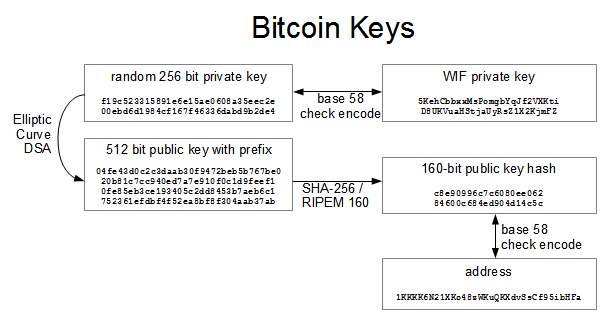
crypto-lite Gem Update - New Examples / Cookbook - Bitcoin (Base58) Address Generation form the (Elliptic Curve) Public Key Made Easy - Inside the Magic Bubble Machine : r/ruby



.png)